Proportional Document Governance Through Risk-Based Classification
Proportionale Dokumenten-Governance durch risikobasierte Klassifizierung
Governanca Proporcional de Documentos atraves de Classificacao Baseada em Risco
The Three-Level Model: Operational, Institutional, and Forensic Regulatory Standards in the WINDI System
Das Drei-Stufen-Modell: Operationelle, Institutionelle und Forensisch-Regulatorische Standards im WINDI System
O Modelo de Tres Niveis: Padroes Operacionais, Institucionais e Forenses Regulatorios no Sistema WINDI
This technical report presents the WINDI Governance Engine's three-level document classification model, a risk-proportional approach to institutional document governance. Rather than applying uniform security measures to all documents, the system implements graduated governance layers—Operational (LOW), Institutional (MEDIUM), and Forensic Regulatory (HIGH)—where each level enforces requirements proportional to the document's institutional impact and regulatory significance.
Dieser technische Bericht prasentiert das Drei-Stufen-Dokumentenklassifizierungsmodell der WINDI Governance Engine, einen risikoproportionalen Ansatz zur institutionellen Dokumenten-Governance. Anstatt einheitliche Sicherheitsmassnahmen auf alle Dokumente anzuwenden, implementiert das System abgestufte Governance-Ebenen—Operationell (LOW), Institutionell (MEDIUM) und Forensisch-Regulatorisch (HIGH)—wobei jede Ebene Anforderungen proportional zur institutionellen Auswirkung und regulatorischen Bedeutung des Dokuments durchsetzt.
Este relatorio tecnico apresenta o modelo de classificacao de documentos de tres niveis do Motor de Governanca WINDI, uma abordagem proporcional ao risco para governanca de documentos institucionais. Em vez de aplicar medidas de seguranca uniformes a todos os documentos, o sistema implementa camadas de governanca graduadas—Operacional (LOW), Institucional (MEDIUM) e Forense Regulatorio (HIGH)—onde cada nivel aplica requisitos proporcionais ao impacto institucional e significancia regulatoria do documento.
The architecture is validated through a production deployment on German infrastructure (Strato), with the first regulatory-grade submission (REG-20260201-0001) demonstrating complete chain integrity, tamper evidence, and metadata enforcement. The system's Institutional Security Profiles (ISP) enable per-organisation governance configuration, supporting environments from operational daily workflows (Deutsche Bahn) to central banking supervision (BIS-Style).
Die Architektur wird durch eine Produktionsbereitstellung auf deutscher Infrastruktur (Strato) validiert, wobei die erste regulatorische Einreichung (REG-20260201-0001) vollstandige Kettenintegritat, Manipulationsnachweis und Metadatendurchsetzung demonstriert. Die institutionellen Sicherheitsprofile (ISP) des Systems ermoglichen eine organisationsspezifische Governance-Konfiguration.
A arquitetura e validada atraves de implantacao em producao na infraestrutura alema (Strato), com a primeira submissao de grau regulatorio (REG-20260201-0001) demonstrando integridade completa da cadeia, evidencia de adulteracao e aplicacao de metadados. Os Perfis de Seguranca Institucional (ISP) do sistema permitem configuracao de governanca por organizacao.
Section 1: Introduction — The Problem of Uniform Governance
Abschnitt 1: Einfuhrung — Das Problem einheitlicher Governance
Secao 1: Introducao — O Problema da Governanca Uniforme
Institutional environments produce documents with vastly different risk profiles. An internal operational memo at a transport company carries fundamentally different governance requirements than a regulatory submission to a central banking authority. Yet traditional document management systems typically apply either no governance controls or enforce uniform, heavy-weight compliance mechanisms across all document types.
Institutionelle Umgebungen produzieren Dokumente mit sehr unterschiedlichen Risikoprofilen. Ein internes operatives Memo bei einem Transportunternehmen hat grundlegend andere Governance-Anforderungen als eine regulatorische Einreichung bei einer Zentralbank-Behorde. Traditionelle Dokumentenmanagementsysteme wenden jedoch typischerweise entweder keine Governance-Kontrollen an oder erzwingen einheitliche, schwergewichtige Compliance-Mechanismen uber alle Dokumenttypen hinweg.
Ambientes institucionais produzem documentos com perfis de risco vastamente diferentes. Um memorando operacional interno em uma empresa de transporte carrega requisitos de governanca fundamentalmente diferentes de uma submissao regulatoria a uma autoridade bancaria central. No entanto, sistemas tradicionais de gerenciamento de documentos tipicamente aplicam ou nenhum controle de governanca ou impoe mecanismos de conformidade uniformes e pesados em todos os tipos de documento.
This binary approach creates two failure modes. Under-governance exposes institutions to compliance risks and lacks traceability when it matters most. Over-governance burdens daily operations with unnecessary overhead, creating friction that leads to workarounds and shadow processes that ultimately undermine governance altogether.
Dieser binare Ansatz schafft zwei Fehlermodi. Unter-Governance setzt Institutionen Compliance-Risiken aus und fehlt Ruckverfolgbarkeit, wenn es am wichtigsten ist. Uber-Governance belastet den taglichen Betrieb mit unnotigem Overhead und schafft Reibung, die zu Workarounds und Schattenprozessen fuhrt, die letztendlich die Governance insgesamt untergraben.
Esta abordagem binaria cria dois modos de falha. Sub-governanca expoe instituicoes a riscos de conformidade e carece de rastreabilidade quando mais importa. Sobre-governanca sobrecarrega operacoes diarias com overhead desnecessario, criando atrito que leva a solucoes alternativas e processos sombra que finalmente minam a governanca por completo.
The WINDI system resolves this tension through proportional governance—a risk-based classification model where the depth of metadata requirements, audit trails, and integrity mechanisms scales with the document's institutional impact.
Das WINDI System lost diese Spannung durch proportionale Governance—ein risikobasiertes Klassifizierungsmodell, bei dem die Tiefe der Metadatenanforderungen, Audit-Trails und Integritatsmechanismen mit der institutionellen Auswirkung des Dokuments skaliert.
O sistema WINDI resolve esta tensao atraves de governanca proporcional—um modelo de classificacao baseado em risco onde a profundidade dos requisitos de metadados, trilhas de auditoria e mecanismos de integridade escala com o impacto institucional do documento.
The greater the institutional impact, the greater the requirement for metadata completeness and traceability.
Je grosser die institutionelle Auswirkung, desto grosser die Anforderung an Metadatenvollstandigkeit und Nachvollziehbarkeit.
Quanto maior o impacto institucional, maior o requisito de completude de metadados e rastreabilidade.
Section 2: The Three-Level Governance Model
Abschnitt 2: Das Drei-Stufen-Governance-Modell
Secao 2: O Modelo de Governanca de Tres Niveis
The WINDI Governance Engine implements three distinct governance levels, each designed for a specific class of institutional document. The levels are not arbitrary tiers but represent fundamentally different governance philosophies, from invisible facilitation to forensic enforcement.
Die WINDI Governance Engine implementiert drei verschiedene Governance-Ebenen, jede fur eine spezifische Klasse institutioneller Dokumente konzipiert. Die Ebenen sind keine willkurlichen Stufen, sondern reprasentieren fundamental unterschiedliche Governance-Philosophien, von unsichtbarer Erleichterung bis zur forensischen Durchsetzung.
O Motor de Governanca WINDI implementa tres niveis distintos de governanca, cada um projetado para uma classe especifica de documento institucional. Os niveis nao sao camadas arbitrarias, mas representam filosofias de governanca fundamentalmente diferentes, desde facilitacao invisivel ate aplicacao forense.
2.1 LOW — Operational Standard
2.1 LOW — Operativer Standard
2.1 LOW — Padrao Operacional
The Operational Standard is designed for daily institutional workflows where governance should be invisible. Internal memos, routine communications, and operational documents pass through the system without metadata requirements, submission identifiers, or forensic sealing. The governance layer exists but does not impose.
Der operative Standard ist fur tagliche institutionelle Workflows konzipiert, bei denen Governance unsichtbar sein sollte. Interne Memos, Routinekommunikation und operative Dokumente passieren das System ohne Metadatenanforderungen, Einreichungs-IDs oder forensische Versiegelung. Die Governance-Schicht existiert, aber sie zwingt nicht auf.
O Padrao Operacional e projetado para fluxos de trabalho institucionais diarios onde a governanca deve ser invisivel. Memorandos internos, comunicacoes de rotina e documentos operacionais passam pelo sistema sem requisitos de metadados, identificadores de submissao ou selagem forense. A camada de governanca existe mas nao impoe.
This level acknowledges a critical insight: not every document requires traceability. Applying regulatory overhead to routine operations creates institutional fatigue and diminishes the perceived value of governance when it truly matters.
Diese Ebene erkennt eine kritische Erkenntnis an: Nicht jedes Dokument erfordert Nachvollziehbarkeit. Die Anwendung regulatorischen Overheads auf Routineoperationen schafft institutionelle Ermudung und vermindert den wahrgenommenen Wert von Governance, wenn sie wirklich wichtig ist.
Este nivel reconhece um insight critico: nem todo documento requer rastreabilidade. Aplicar overhead regulatorio a operacoes de rotina cria fadiga institucional e diminui o valor percebido da governanca quando ela realmente importa.
2.2 MEDIUM — Institutional Standard
2.2 MEDIUM — Institutioneller Standard
2.2 MEDIUM — Padrao Institucional
The Institutional Standard occupies the critical middle ground between operational fluidity and regulatory rigour. Documents at this level carry institutional weight—policy notes, compliance reports, formal inter-departmental communications—and require structured metadata that establishes organisational accountability without imposing forensic-grade controls.
Der institutionelle Standard besetzt das kritische Mittelfeld zwischen operativer Fluiditat und regulatorischer Strenge. Dokumente auf dieser Ebene tragen institutionelles Gewicht—Richtliniennotizen, Compliance-Berichte, formelle inter-departementale Kommunikation—und erfordern strukturierte Metadaten, die organisatorische Verantwortlichkeit etablieren, ohne forensische Kontrollen aufzuerlegen.
O Padrao Institucional ocupa o terreno critico entre fluidez operacional e rigor regulatorio. Documentos neste nivel carregam peso institucional—notas de politica, relatorios de conformidade, comunicacoes inter-departamentais formais—e requerem metadados estruturados que estabelecem responsabilidade organizacional sem impor controles de grau forense.
MEDIUM-level governance enforces institutional metadata (issuing authority, document purpose, confidentiality classification, validation status) and maintains standard audit trails. It does not, however, generate submission identifiers, compute integrity hashes, or create forensic registry entries. The distinction is deliberate: institutional accountability is not the same as regulatory traceability.
MEDIUM-Level Governance erzwingt institutionelle Metadaten (ausstellende Behorde, Dokumentzweck, Vertraulichkeitsklassifizierung, Validierungsstatus) und pflegt Standard-Audit-Trails. Sie generiert jedoch keine Einreichungs-IDs, berechnet keine Integritäts-Hashes oder erstellt keine forensischen Registry-Eintrage. Die Unterscheidung ist beabsichtigt: institutionelle Verantwortlichkeit ist nicht dasselbe wie regulatorische Ruckverfolgbarkeit.
Governanca nivel MEDIUM aplica metadados institucionais (autoridade emissora, proposito do documento, classificacao de confidencialidade, status de validacao) e mantem trilhas de auditoria padrao. No entanto, nao gera identificadores de submissao, calcula hashes de integridade ou cria entradas de registro forense. A distincao e deliberada: responsabilidade institucional nao e o mesmo que rastreabilidade regulatoria.
2.3 HIGH — Forensic Regulatory
2.3 HIGH — Forensisch-Regulatorisch
2.3 HIGH — Forense Regulatorio
The Forensic Regulatory level implements the full governance apparatus. Designed for environments where regulatory compliance demands complete traceability—central banking supervision, statistical reporting frameworks (SDMX), EU AI Act compliance submissions—this level enforces a strict invariant: a document cannot be generated unless all required regulatory metadata is present and validated.
Die forensisch-regulatorische Ebene implementiert den vollstandigen Governance-Apparat. Konzipiert fur Umgebungen, in denen regulatorische Compliance vollstandige Ruckverfolgbarkeit erfordert—Zentralbank-Aufsicht, statistische Berichtsrahmen (SDMX), EU AI Act Compliance-Einreichungen—erzwingt diese Ebene eine strikte Invariante: Ein Dokument kann nicht generiert werden, es sei denn, alle erforderlichen regulatorischen Metadaten sind vorhanden und validiert.
O nivel Forense Regulatorio implementa o aparato completo de governanca. Projetado para ambientes onde conformidade regulatoria exige rastreabilidade completa—supervisao de bancos centrais, frameworks de relatorios estatisticos (SDMX), submissoes de conformidade EU AI Act—este nivel aplica uma invariante estrita: um documento nao pode ser gerado a menos que todos os metadados regulatorios requeridos estejam presentes e validados.
Each HIGH-level generation produces a sealed submission package containing a unique Submission ID, a configuration hash binding the document to the exact governance policy version, an integrity hash for tamper evidence, and a forensic registry entry enabling retrospective audit. The chain of integrity is preserved from generation through archival.
Jede HIGH-Level Generierung produziert ein versiegeltes Einreichungspaket mit einer eindeutigen Submission-ID, einem Konfigurations-Hash, der das Dokument an die exakte Governance-Richtlinienversion bindet, einem Integritäts-Hash fur Manipulationsnachweis und einem forensischen Registry-Eintrag, der retrospektive Audits ermoglicht. Die Integritatskette wird von der Generierung bis zur Archivierung bewahrt.
Cada geracao HIGH-level produz um pacote de submissao selado contendo um ID de Submissao unico, um hash de configuracao vinculando o documento a versao exata da politica de governanca, um hash de integridade para evidencia de adulteracao e uma entrada de registro forense permitindo auditoria retrospectiva. A cadeia de integridade e preservada desde a geracao ate o arquivamento.
Section 3: Comparative Analysis of Governance Levels
Abschnitt 3: Vergleichende Analyse der Governance-Ebenen
Secao 3: Analise Comparativa dos Niveis de Governanca
The following matrix presents a comprehensive comparison of governance features across the three levels, demonstrating the proportional escalation of requirements as institutional impact increases.
Die folgende Matrix prasentiert einen umfassenden Vergleich der Governance-Funktionen uber die drei Ebenen hinweg und demonstriert die proportionale Eskalation der Anforderungen bei steigender institutioneller Auswirkung.
A matriz a seguir apresenta uma comparacao abrangente das funcionalidades de governanca atraves dos tres niveis, demonstrando a escalacao proporcional de requisitos conforme o impacto institucional aumenta.
| Governance Feature | LOW | MEDIUM | HIGH |
|---|---|---|---|
| Mandatory Metadata | — | Y Institutional (7) | Y Regulatory (10) |
| Metadata Block Schema | — | Institutional | SDMX-aligned |
| Policy Version | — | Y | Y |
| Configuration Hash | — | — | Y SHA-256 |
| Submission ID | — | — | Y REG-* |
| Integrity Hash | — | — | Y SHA-256 |
| Forensic Registry | — | — | Y Full chain |
| Audit Trail | — | Standard | Full forensic |
| Watermark | — | Discreet footer | Header + footer |
| Generation Blocking | — | Y Missing metadata | Y Missing metadata |
| Tamper Evidence | — | — | Y Seal + verify |
Section 4: Institutional Security Profiles (ISP)
Abschnitt 4: Institutionelle Sicherheitsprofile (ISP)
Secao 4: Perfis de Seguranca Institucional (ISP)
Each organisation deploying the WINDI system operates under a configurable Institutional Security Profile that determines its default governance level, permitted upgrades, minimum enforcement thresholds, and document-type overrides. The ISP transforms WINDI from a static governance engine into configurable institutional infrastructure.
Jede Organisation, die das WINDI System einsetzt, operiert unter einem konfigurierbaren institutionellen Sicherheitsprofil, das ihre Standard-Governance-Ebene, erlaubte Upgrades, minimale Durchsetzungsschwellen und Dokumenttyp-Uberschreibungen bestimmt. Das ISP transformiert WINDI von einer statischen Governance-Engine in konfigurierbare institutionelle Infrastruktur.
Cada organizacao que implanta o sistema WINDI opera sob um Perfil de Seguranca Institucional configuravel que determina seu nivel de governanca padrao, upgrades permitidos, limites minimos de aplicacao e substituicoes de tipo de documento. O ISP transforma o WINDI de um motor de governanca estatico em infraestrutura institucional configuravel.
4.1 Active Profiles in Production
4.1 Aktive Profile in Produktion
4.1 Perfis Ativos em Producao
- Deutsche Bahn AG — Operational (LOW)
- Transport operator. Default governance: LOW. Operational documents flow without metadata constraints. Manual upgrade to HIGH permitted for regulatory submissions.
- Transportbetreiber. Standard-Governance: LOW. Operative Dokumente fliessen ohne Metadatenbeschrankungen. Manuelles Upgrade auf HIGH fur regulatorische Einreichungen erlaubt.
- Operadora de transporte. Governanca padrao: LOW. Documentos operacionais fluem sem restricoes de metadados. Upgrade manual para HIGH permitido para submissoes regulatorias.
- BIS-Style Regulatory Authority — Forensic (HIGH)
- Central banking supervision model. Default governance: HIGH. All documents require complete SDMX-aligned regulatory metadata. No downgrade permitted below HIGH.
- Zentralbank-Aufsichtsmodell. Standard-Governance: HIGH. Alle Dokumente erfordern vollstandige SDMX-ausgerichtete regulatorische Metadaten. Kein Downgrade unter HIGH erlaubt.
- Modelo de supervisao de banco central. Governanca padrao: HIGH. Todos os documentos requerem metadados regulatorios completos alinhados ao SDMX. Nenhum downgrade permitido abaixo de HIGH.
- Bundesregierung — Institutional (MEDIUM)
- Federal government institutional profile. Default governance: MEDIUM. Policy notes and formal communications require institutional metadata. Regulatory submissions escalate to HIGH. No downgrade below MEDIUM.
- Bundesregierung institutionelles Profil. Standard-Governance: MEDIUM. Richtliniennotizen und formelle Kommunikation erfordern institutionelle Metadaten. Regulatorische Einreichungen eskalieren auf HIGH. Kein Downgrade unter MEDIUM.
- Perfil institucional do governo federal. Governanca padrao: MEDIUM. Notas de politica e comunicacoes formais requerem metadados institucionais. Submissoes regulatorias escalam para HIGH. Nenhum downgrade abaixo de MEDIUM.
4.2 ISP Governance Configuration
4.2 ISP Governance-Konfiguration
4.2 Configuracao de Governanca ISP
{
"organization_name": "Bundesregierung (Model)",
"isp_profile": "bundesregierung",
"governance": {
"default_level": "MEDIUM",
"policies": {
"manual_upgrade": ["HIGH"],
"no_downgrade_min_level": "MEDIUM"
}
},
"document_type_overrides": {
"internal_memo": "MEDIUM",
"policy_note": "MEDIUM",
"regulatory_submission": "HIGH"
}
}
The no-downgrade enforcement mechanism ensures that organisations operating at MEDIUM cannot accidentally generate LOW-governance documents, preserving institutional accountability as a floor rather than an option.
Der No-Downgrade-Durchsetzungsmechanismus stellt sicher, dass Organisationen, die auf MEDIUM operieren, nicht versehentlich LOW-Governance-Dokumente generieren konnen, wodurch institutionelle Verantwortlichkeit als Mindeststandard und nicht als Option erhalten bleibt.
O mecanismo de aplicacao no-downgrade garante que organizacoes operando em MEDIUM nao possam acidentalmente gerar documentos LOW-governance, preservando responsabilidade institucional como piso em vez de opcao.
Section 5: System Dashboard — Production Environment
Abschnitt 5: System-Dashboard — Produktionsumgebung
Secao 5: Dashboard do Sistema — Ambiente de Producao
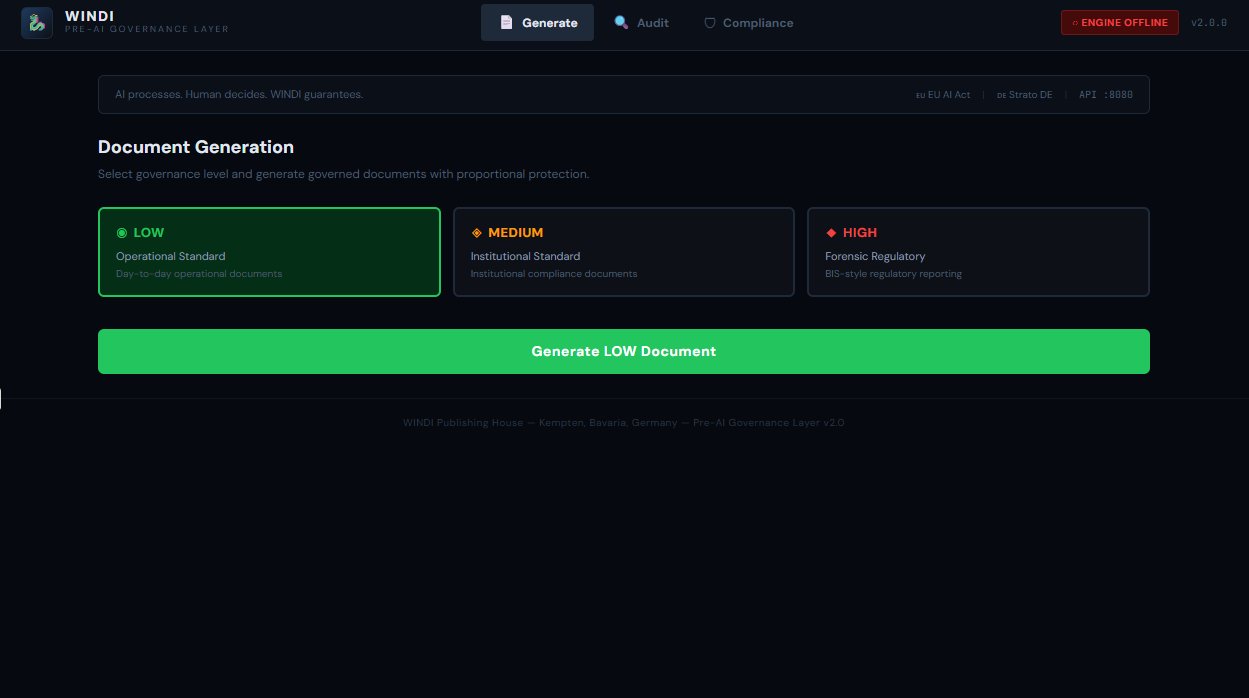
The WINDI Governance Dashboard provides real-time visibility into the governance engine's operational state. The interface exposes document generation controls with level selection, the audit registry with submission chain integrity, and compliance monitoring with invariant validation status.
Das WINDI Governance Dashboard bietet Echtzeit-Einblick in den Betriebszustand der Governance Engine. Die Schnittstelle zeigt Dokumentengenerierungskontrollen mit Ebenenauswahl, das Audit-Register mit Einreichungsketten-Integritat und Compliance-Uberwachung mit Invariantenvalidierungsstatus.
O Dashboard de Governanca WINDI fornece visibilidade em tempo real do estado operacional do motor de governanca. A interface expoe controles de geracao de documentos com selecao de nivel, o registro de auditoria com integridade da cadeia de submissao e monitoramento de conformidade com status de validacao de invariantes.
Section 6: Validation — First Regulatory Submission
Abschnitt 6: Validierung — Erste Regulatorische Einreichung
Secao 6: Validacao — Primeira Submissao Regulatoria
On 01 February 2026, the WINDI Governance Engine produced its first sealed regulatory submission, validating the complete HIGH-level governance chain in a production environment. The submission demonstrates end-to-end functionality: metadata validation, submission identifier generation, configuration binding, integrity hashing, tamper evidence sealing, and forensic registry entry.
Am 01. Februar 2026 produzierte die WINDI Governance Engine ihre erste versiegelte regulatorische Einreichung und validierte die vollstandige HIGH-Level Governance-Kette in einer Produktionsumgebung. Die Einreichung demonstriert End-to-End-Funktionalitat: Metadatenvalidierung, Einreichungs-ID-Generierung, Konfigurationsbindung, Integritäts-Hashing, Manipulationsnachweisversiegelung und forensischer Registry-Eintrag.
Em 01 de fevereiro de 2026, o Motor de Governanca WINDI produziu sua primeira submissao regulatoria selada, validando a cadeia completa de governanca HIGH-level em ambiente de producao. A submissao demonstra funcionalidade de ponta a ponta: validacao de metadados, geracao de identificador de submissao, vinculacao de configuracao, hashing de integridade, selagem de evidencia de adulteracao e entrada de registro forense.
// Submission Package submission_id: REG-20260201-0001 level: HIGH (Forensic Regulatory) profile: BIS-Style (Model) policy_version: 2.0.0 config_hash: 0eaa119c63bc1c59...dcfe0d84 integrity_hash: dd68612cf5dc60fd...faa600e4 chain_status: COMPLETE sealed_at: 2026-02-01T08:58:11Z entity: European Central Bank (Model) infrastructure: German (Strato), GDPR-compliant
This submission represents the proof that the WINDI governance model operates beyond theoretical architecture. The system enforces metadata completeness, generates cryptographic integrity evidence, and maintains a forensic registry—all on production infrastructure subject to European data protection regulations.
Diese Einreichung reprasentiert den Beweis, dass das WINDI Governance-Modell uber theoretische Architektur hinaus operiert. Das System erzwingt Metadatenvollstandigkeit, generiert kryptografische Integritatsnachweise und pflegt ein forensisches Register—alles auf Produktionsinfrastruktur, die europaischen Datenschutzvorschriften unterliegt.
Esta submissao representa a prova de que o modelo de governanca WINDI opera alem da arquitetura teorica. O sistema aplica completude de metadados, gera evidencia de integridade criptografica e mantem um registro forense—tudo em infraestrutura de producao sujeita a regulamentacoes europeias de protecao de dados.
Section 7: Academic Significance and Contribution
Abschnitt 7: Akademische Bedeutung und Beitrag
Secao 7: Significancia Academica e Contribuicao
The three-level governance model presented in this report addresses a gap in the current literature on AI-assisted document generation. While existing frameworks focus on either full compliance enforcement or no governance at all, the WINDI approach demonstrates that proportional governance is both technically feasible and architecturally sound.
Das in diesem Bericht prasentierte Drei-Stufen-Governance-Modell adressiert eine Lucke in der aktuellen Literatur zur KI-unterstutzten Dokumentengenerierung. Wahrend bestehende Frameworks sich entweder auf vollstandige Compliance-Durchsetzung oder gar keine Governance konzentrieren, demonstriert der WINDI-Ansatz, dass proportionale Governance sowohl technisch machbar als auch architektonisch solide ist.
O modelo de governanca de tres niveis apresentado neste relatorio aborda uma lacuna na literatura atual sobre geracao de documentos assistida por IA. Enquanto frameworks existentes focam em aplicacao de conformidade completa ou nenhuma governanca, a abordagem WINDI demonstra que governanca proporcional e tanto tecnicamente viavel quanto arquitetonicamente solida.
The model's core contributions are threefold:
Die Kernbeitrage des Modells sind dreifach:
As contribuicoes centrais do modelo sao tres:
- Graduated governance: It establishes that document governance can be graduated rather than binary, with enforcement depth scaling to institutional risk. Abgestufte Governance: Es etabliert, dass Dokumenten-Governance abgestuft statt binar sein kann, wobei die Durchsetzungstiefe mit dem institutionellen Risiko skaliert. Governanca graduada: Estabelece que governanca de documentos pode ser graduada em vez de binaria, com profundidade de aplicacao escalando com o risco institucional.
- Regulatory-grade traceability: It proves that regulatory-grade traceability—including cryptographic integrity chains and forensic registries—can be implemented as a system layer rather than an afterthought. Regulatorische Ruckverfolgbarkeit: Es beweist, dass regulatorische Ruckverfolgbarkeit—einschliesslich kryptografischer Integritatsketten und forensischer Register—als Systemschicht implementiert werden kann, statt als nachtraglicher Gedanke. Rastreabilidade de grau regulatorio: Prova que rastreabilidade de grau regulatorio—incluindo cadeias de integridade criptografica e registros forenses—pode ser implementada como camada de sistema em vez de pensamento posterior.
- Per-organisation configuration: The ISP mechanism demonstrates that per-organisation governance configuration is viable in production, enabling a single platform to serve operational, institutional, and regulatory environments simultaneously. Organisations-spezifische Konfiguration: Der ISP-Mechanismus demonstriert, dass organisations-spezifische Governance-Konfiguration in Produktion praktikabel ist und einer einzelnen Plattform ermoglicht, operative, institutionelle und regulatorische Umgebungen gleichzeitig zu bedienen. Configuracao por organizacao: O mecanismo ISP demonstra que configuracao de governanca por organizacao e viavel em producao, permitindo que uma unica plataforma sirva ambientes operacionais, institucionais e regulatorios simultaneamente.
These contributions align with the EU AI Act's emphasis on risk-based regulation and support the broader thesis of the WINDI project: that a pre-AI governance layer can guarantee proportional institutional compliance while preserving human decision-making authority.
Diese Beitrage entsprechen dem Schwerpunkt des EU AI Act auf risikobasierter Regulierung und unterstutzen die breitere These des WINDI-Projekts: dass eine Pre-AI-Governance-Schicht proportionale institutionelle Compliance garantieren kann, wahrend die menschliche Entscheidungsbefugnis erhalten bleibt.
Estas contribuicoes alinham-se com a enfase do EU AI Act em regulacao baseada em risco e apoiam a tese mais ampla do projeto WINDI: que uma camada de governanca pre-IA pode garantir conformidade institucional proporcional enquanto preserva a autoridade de decisao humana.
AI processes. Human decides. WINDI guarantees proportionally.
KI verarbeitet. Mensch entscheidet. WINDI garantiert proportional.
IA processa. Humano decide. WINDI garante proporcionalmente.
Section 8: System Architecture Overview
Abschnitt 8: Systemarchitektur-Uberblick
Secao 8: Visao Geral da Arquitetura do Sistema
+-----------------------------------------------------+
| A4 DESK BABEL UI |
| (Port 8085 | TipTap) |
| +----------+ +----------+ +------------------+ |
| | Editor | | Chat | | Level Selector | |
| | DE/EN/PT | | Triling | | LOW MED HIGH | |
| +----------+ +----------+ +------------------+ |
+----------------------+------------------------------+
|
v
+-----------------------------------------------------+
| WINDI GOVERNANCE API |
| (Port 8080) |
| |
| +------------+ +-----------+ +------------------+ |
| | ISP Loader | | Validator | | Submission ID | |
| | | | | | Generator | |
| +-----+------+ +-----+-----+ +--------+---------+ |
| | | | |
| +-----v--------------v-----------------v---------+ |
| | Governance Engine Core | |
| | +---------+ +----------+ +--------------+ | |
| | | Tamper | | Registry | | Dashboard | | |
| | | Evidence | | | | + Audit | | |
| | +---------+ +----------+ +--------------+ | |
| +------------------------------------------------+ |
+----------------------+------------------------------+
|
v
+-----------------------------------------------------+
| ISP PROFILES |
| +--------------+ +------------+ +--------------+ |
| | Deutsche Bahn| | BIS-Style | |Bundesregierung| |
| | [G] LOW | | [R] HIGH | | [Y] MEDIUM | |
| +--------------+ +------------+ +--------------+ |
+-----------------------------------------------------+
Section 9: Integration Testing — Dragon Council Validation
Abschnitt 9: Integrationstests — Dragon Council Validierung
Secao 9: Testes de Integracao — Validacao Dragon Council
The governance engine was validated through the Dragon Council integration test suite, which exercises all critical governance paths. All eight tests pass in the production environment, confirming operational readiness across all governance levels.
Die Governance Engine wurde durch die Dragon Council Integrationstestsuite validiert, die alle kritischen Governance-Pfade durchlauft. Alle acht Tests bestehen in der Produktionsumgebung und bestatigen die Betriebsbereitschaft uber alle Governance-Ebenen hinweg.
O motor de governanca foi validado atraves da suite de testes de integracao Dragon Council, que exercita todos os caminhos criticos de governanca. Todos os oito testes passam no ambiente de producao, confirmando prontidao operacional em todos os niveis de governanca.
================================================== WINDI Dragon Council Integration Test ================================================== PASS 1. Deutsche Bahn LOW passes without metadata PASS 2. BIS-Style HIGH blocked without metadata PASS 3. BIS-Style HIGH approved with full metadata PASS 4. No-downgrade enforcement PASS 5. Tamper evidence: seal + verify + detect PASS 6. Registry: register + query + stats PASS 7. Audit dashboard: overview + integrity + entity PASS 8. Rejects invalid allowed values ================================================== Results: 8/8 passed, 0 failed Dragon Council merge: VALIDATED AI processes. Human decides. WINDI guarantees.
Section 10: Institutional Identity Governance Layer
Abschnitt 10: Institutionelle Identitats-Governance-Schicht
Secao 10: Camada de Governanca de Identidade Institucional
Milestone: 01 February 2026 — Dragon Council Decision (Guardian + Architect)
Meilenstein: 01. Februar 2026 — Dragon Council Entscheidung (Guardian + Architect)
Marco: 01 de Fevereiro de 2026 — Decisao Dragon Council (Guardian + Architect)
During the deployment of the MEDIUM governance level, a critical architectural discovery emerged from a real-world test case: the generation of a formal letter styled after Banco do Brasil S.A. The system correctly produced institutional language, formal structure, and even referenced the institution's values (Integridade, Sustentabilidade, Performance) — but this raised a fundamental governance question: when does institutional language simulation require governance controls?
Wahrend der Bereitstellung der MEDIUM-Governance-Ebene entstand eine kritische architektonische Entdeckung aus einem realen Testfall: die Generierung eines formellen Briefes im Stil der Banco do Brasil S.A. Das System produzierte korrekt institutionelle Sprache, formelle Struktur und verwies sogar auf die Werte der Institution — aber dies warf eine fundamentale Governance-Frage auf: Wann erfordert die Simulation institutioneller Sprache Governance-Kontrollen?
Durante a implantacao do nivel de governanca MEDIUM, uma descoberta arquitetonica critica emergiu de um caso de teste real: a geracao de uma carta formal estilizada apos o Banco do Brasil S.A. O sistema produziu corretamente linguagem institucional, estrutura formal e ate referenciou os valores da instituicao (Integridade, Sustentabilidade, Performance) — mas isso levantou uma questao fundamental de governanca: quando a simulacao de linguagem institucional requer controles de governanca?
The answer became the Identity Governance Layer — a licensing mechanism integrated directly into ISP Profiles that controls whether an institution's identity (logo, letterhead, tone, values, official address) may be used in generated documents. This transforms MEDIUM from a simple metadata layer into an institutional identity governance platform.
Die Antwort wurde die Identity Governance Layer — ein Lizenzierungsmechanismus, der direkt in ISP-Profile integriert ist und kontrolliert, ob die Identitat einer Institution (Logo, Briefkopf, Ton, Werte, offizielle Adresse) in generierten Dokumenten verwendet werden darf. Dies transformiert MEDIUM von einer einfachen Metadatenschicht in eine institutionelle Identitats-Governance-Plattform.
A resposta se tornou a Camada de Governanca de Identidade — um mecanismo de licenciamento integrado diretamente nos Perfis ISP que controla se a identidade de uma instituicao (logo, papel timbrado, tom, valores, endereco oficial) pode ser usada em documentos gerados. Isso transforma MEDIUM de uma simples camada de metadados em uma plataforma de governanca de identidade institucional.
10.1 The Identity License Schema
10.1 Das Identity-License-Schema
10.1 O Schema de Licenca de Identidade
Each ISP Profile now contains an identity_license block that declares the authorisation status for institutional identity usage. The system recognises five statuses, each triggering different governance behaviours automatically:
Jedes ISP-Profil enthalt nun einen identity_license-Block, der den Autorisierungsstatus fur die Nutzung der institutionellen Identitat deklariert. Das System erkennt funf Status, die jeweils unterschiedliche Governance-Verhaltensweisen automatisch auslosen:
Cada Perfil ISP agora contem um bloco identity_license que declara o status de autorizacao para uso de identidade institucional. O sistema reconhece cinco status, cada um acionando diferentes comportamentos de governanca automaticamente:
"identity_license": { "status": "model_only" | "authorized" | "pending" | "expired" | "revoked", "authorized_by": "Diretoria de Comunicacao Corporativa", "authorization_ref": "CONTRATO-BB-WINDI-2026-001", "authorization_hash": "sha256 of authorization document", "valid_from": "2026-03-01", "valid_until": "2027-02-28", "scope": { "logo": true | false, "letterhead": true | false, "institutional_tone": true, "values_reference": true, "official_address": true | false }, "restrictions": ["Model/simulation use only"] }
10.2 Behaviour Matrix
10.2 Verhaltensmatrix
10.2 Matriz de Comportamento
The governance engine evaluates the identity license at generation time, including automatic expiration checking for authorized licenses. The following matrix defines system behaviour for each license status:
Die Governance-Engine bewertet die Identitatslizenz zum Generierungszeitpunkt, einschliesslich automatischer Ablaufprufung fur autorisierte Lizenzen. Die folgende Matrix definiert das Systemverhalten fur jeden Lizenzstatus:
O motor de governanca avalia a licenca de identidade no momento da geracao, incluindo verificacao automatica de expiracao para licencas autorizadas. A matriz a seguir define o comportamento do sistema para cada status de licenca:
| License Status | Logo | Institutional Tone | Disclaimer | Audit Category |
|---|---|---|---|---|
| model_only | x | Y | Y Required | model_simulation |
| pending | x | Y | Y Required | pending_license |
| authorized | Y per scope | Y | — Optional | licensed_usage |
| expired | x | Y | Y Required | license_expired |
| revoked | x | x Restricted | Y Required | license_revoked |
10.3 Automatic Disclaimer (Trilingual)
10.3 Automatischer Disclaimer (Trilingual)
10.3 Disclaimer Automatico (Trilingue)
When a document is generated under model_only, pending, expired, or revoked status, the system automatically includes a disclaimer in the governance response:
Wenn ein Dokument unter model_only, pending, expired oder revoked Status generiert wird, fugt das System automatisch einen Disclaimer in die Governance-Antwort ein:
Quando um documento e gerado sob status model_only, pending, expired ou revoked, o sistema automaticamente inclui um disclaimer na resposta de governanca:
DE: Dieses Dokument verwendet institutionelle Sprache zu Modell- oder Simulationszwecken. Es handelt sich nicht um ein offizielles Dokument der genannten Institution.
EN: This document uses institutional language for model or simulation purposes. It is not an official document issued by the mentioned institution.
PT: Este documento utiliza linguagem institucional para fins de modelo ou simulacao. Nao se trata de documento oficial emitido pela instituicao mencionada.
10.4 Live Production Response
10.4 Live-Produktionsantwort
10.4 Resposta de Producao Ao Vivo
The following is the actual API response from the production Governance Engine on 01 February 2026, showing the identity_governance block integrated into a MEDIUM-level generation for the Bundesregierung ISP profile:
Das Folgende ist die tatsachliche API-Antwort der Produktions-Governance-Engine vom 01. Februar 2026, die den identity_governance-Block zeigt, der in eine MEDIUM-Level-Generierung fur das Bundesregierung ISP-Profil integriert ist:
O seguinte e a resposta real da API do Motor de Governanca de producao em 01 de Fevereiro de 2026, mostrando o bloco identity_governance integrado em uma geracao nivel MEDIUM para o perfil ISP Bundesregierung:
{
"status": "APPROVED",
"governance_level": "MEDIUM",
"governance_name": "Institutional Standard",
"isp_profile": "bundesregierung",
"metadata": { /* 7 institutional fields */ },
"identity_governance": {
"institution": "Bundesregierung (Model)",
"license_status": "model_only",
"logo_allowed": false,
"disclaimer_required": true,
"disclaimer_text": "This document uses institutional language
for model or simulation purposes...",
"audit_category": "model_simulation",
"restrictions": [
"Model/simulation use only",
"No official government identity permitted",
"Disclaimer required on all documents"
]
}
}
10.5 Architectural Significance
10.5 Architektonische Bedeutung
10.5 Significancia Arquitetonica
The Identity Governance Layer establishes WINDI as the first document generation platform to integrate institutional identity licensing directly into its governance engine. This enables three capabilities not found in existing enterprise document management systems:
Die Identity Governance Layer etabliert WINDI als die erste Dokumentengenerierungsplattform, die institutionelle Identitatslizenzierung direkt in ihre Governance-Engine integriert. Dies ermoglicht drei Fahigkeiten, die in bestehenden Enterprise-Dokumentenmanagementsystemen nicht zu finden sind:
A Camada de Governanca de Identidade estabelece o WINDI como a primeira plataforma de geracao de documentos a integrar licenciamento de identidade institucional diretamente em seu motor de governanca. Isso habilita tres capacidades nao encontradas em sistemas de gerenciamento de documentos empresariais existentes:
- Contractual identity control: Institutions can formally authorise the use of their brand, letterhead, and visual identity within WINDI-governed documents, with automatic expiration and revocation handling. Vertragliche Identitatskontrolle: Institutionen konnen formell die Nutzung ihrer Marke, ihres Briefkopfs und ihrer visuellen Identitat innerhalb von WINDI-gesteuerten Dokumenten autorisieren, mit automatischer Ablauf- und Widerrufsbehandlung. Controle de identidade contratual: Instituicoes podem autorizar formalmente o uso de sua marca, papel timbrado e identidade visual dentro de documentos governados pelo WINDI, com tratamento automatico de expiracao e revogacao.
- Proportional brand protection: Documents that reference real institutions are automatically classified and governed — the system knows the difference between using an institution's language as a model and acting on its behalf. Proportionaler Markenschutz: Dokumente, die auf reale Institutionen verweisen, werden automatisch klassifiziert und gesteuert — das System kennt den Unterschied zwischen der Verwendung der Sprache einer Institution als Modell und dem Handeln in ihrem Namen. Protecao proporcional de marca: Documentos que referenciam instituicoes reais sao automaticamente classificados e governados — o sistema conhece a diferenca entre usar a linguagem de uma instituicao como modelo e agir em seu nome.
- Audit trail for identity usage: Every document generation that involves institutional identity is recorded with its license status, scope, and restrictions, creating an institutional accountability chain. Audit-Trail fur Identitatsnutzung: Jede Dokumentengenerierung, die institutionelle Identitat beinhaltet, wird mit ihrem Lizenzstatus, Umfang und Einschrankungen aufgezeichnet und schafft eine institutionelle Verantwortlichkeitskette. Trilha de auditoria para uso de identidade: Cada geracao de documento que envolve identidade institucional e registrada com seu status de licenca, escopo e restricoes, criando uma cadeia de responsabilidade institucional.
Simulating institutional identity activates institutional governance. The system decides automatically.
Die Simulation institutioneller Identitat aktiviert institutionelle Governance. Das System entscheidet automatisch.
Simular identidade institucional ativa governanca institucional. O sistema decide automaticamente.
Core rule discovered 01 February 2026: Whenever a document mentions or simulates a real institution, governance level must be MEDIUM or higher. This is enforced by the Identity Governance Layer, not by user choice.
Kernregel entdeckt 01. Februar 2026: Wann immer ein Dokument eine reale Institution erwahnt oder simuliert, muss das Governance-Level MEDIUM oder hoher sein. Dies wird von der Identity Governance Layer durchgesetzt, nicht durch Benutzerwahl.
Regra central descoberta 01 de Fevereiro de 2026: Sempre que um documento menciona ou simula uma instituicao real, o nivel de governanca deve ser MEDIUM ou superior. Isso e aplicado pela Camada de Governanca de Identidade, nao por escolha do usuario.